Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing. It is maintained and funded by Offensive Security Ltd. Mati Aharoni, Devon Kearns and Raphaël Hertzog are the core developers. Kali Linux has a dedicated project set-aside for compatibility and porting to specific Android devices, called Kali Linux NetHunter. Kali Linux can be used for many things, but it probably is best known for its ability to penetration test, or “hack,” WPA and WPA2 networks. There are hundreds of Windows applications that claim they can hack WPA; don’t get them! They’re just scams, used by professional hackers, to lure newbie or want-to-be hackers into getting hacked themselves.
There is only one way that hackers get into your network, and that is with a Linux-based OS, a wireless card capable of monitor mode, and aircrack-ng or similar. Also note that, even with these tools, Wi-Fi cracking is not for beginners. Playing with it requires basic knowledge of how WPA authentication works, and moderate familiarity with Kali Linux and its tools, so any hacker who gains access to your network probably is no beginner!
STEPS :
1. Download Kali Linux from here : http://bit.ly/1D2DPLR
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
2. Start Kali Linux and Log in with " root ".
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------
3. Plugin your injection-capable wireless adapter (unless your computer card supports it).
If you’re using Kali in VMware, then you might have to connect the card via the  icon in the device menu.
icon in the device menu.
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
4. Disconnect from all wireless networks, open a Terminal, and type airmon-ng. This will list all of the wireless cards that support monitor (not injection) mode. If no cards are listed, try disconnecting and reconnecting the card and check that it supports monitor mode. You can check if the card supports monitor mode by typing ifconfig in another terminal, if the card is listed in ifconfig, but doesn’t show up in airmon-ng, then the card doesn’t support it.
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
5. Type airmon-ng start followed by the interface of your wireless card. mine is wlan0, so my command would be: airmon-ng start wlan0
The “monitor mode enabled on mon0” message means that the card has successfully been put into monitor mode.
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
6. Type airodump-ng followed by the name of the new monitor interface, which is probablymon0.
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
7. Airo dump will now list all of the wireless networks in your area, and lots of useful information about them. Locate your network or the network that you have permission to penetration test. Once you’ve spotted your network on the ever-populating list, hit Ctrl + Con your keyboard to stop the process. Note the channel of your target network.
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
8. Now Copy the BSSID of the target network.
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
9. Now type this command:
airodump-ng –c [channel] –bssid [bssid] –w /root/Desktop/ [monitor interface]Replace [channel] with the channel of your target network. Paste the network BSSID where [bssid] is, and replace [monitor interface] with the name of your monitor-enabled interface, (mon0).A complete command should look like this:
airodump-ng -c 10 --bssid 00:14:BF:E0:E8:D5 -w /root/Desktop/ mon0
Press Enter.
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
10. Airodump with now monitor only the target network, allowing us to capture more specific information about it. What we’re really doing now is waiting for a device to connect or reconnect to the network, forcing the router to send out the four-way handshake that we need to capture in order to crack the password.
Also, four files should show up on your desktop, this is where the handshake will be saved when captured, so don’t delete them!
But we’re not really going to wait for a device to connect, no, that’s not what impatient hackers do. We’re actually going to use another cool-tool that belongs to the aircrack suite called aireplay-ng, to speed up the process. Instead of waiting for a device to connect, hackers use this tool to force a device to reconnect by sending deauthentication (deauth) packets to the device, making it think that it has to reconnect with the router.
Of course, in order for this tool to work, there has to be someone else connected to the network first, so watch the airodump-ng and wait for a client to show up. It might take a long time, or it might only take a second before the first one shows. If none show up after a lengthy wait, then the network might be empty right now, or you’re to far away from the network.
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
11. Leave airodump-ng running and open a second terminal. In this terminal, type this command:-------------------------------------------------------------------------------------
aireplay-ng –0 2 –a [router bssid] –c [client bssid] mon0The –0 is a short cut for the deauth mode and the 2 is the number of deauth packets to send.
-a indicates the access point (router)’s bssid, replace [router bssid] with the BSSID of the target network, which in my case, is 00:14:BF:E0:E8:D5.
-c indicates the clients BSSID, noted in the previous picture. Replace the [client bssid] with the BSSID of the connected client, this will be listed under “STATION.”
And of course, mon0 merely means the monitor interface, change it if yours is different.
-a indicates the access point (router)’s bssid, replace [router bssid] with the BSSID of the target network, which in my case, is 00:14:BF:E0:E8:D5.
-c indicates the clients BSSID, noted in the previous picture. Replace the [client bssid] with the BSSID of the connected client, this will be listed under “STATION.”
And of course, mon0 merely means the monitor interface, change it if yours is different.
My complete command looks like this:
aireplay-ng –0 2 –a 00:14:BF:E0:E8:D5 –c 4C:EB:42:59:DE:31 mon0
aireplay-ng –0 2 –a 00:14:BF:E0:E8:D5 –c 4C:EB:42:59:DE:31 mon0
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
12. Upon hitting Enter, you’ll see aireplay-ng send the packets, and within moments, you should see this message appear on the airodump-ng screen!
This means that the handshake has been captured, the password is in the hacker’s hands, in some form or another. You can close the aireplay-ng terminal and hit Ctrl + C on the airodump-ng terminal to stop monitoring the network, but don’t close it yet just incase you need some of the information later.
This concludes the external part of this tutorial. From now on, the process is entirely between your computer, and those four files on your Desktop. Actually, the .cap one, that is important. Open a new Terminal, and type in this command:
aircrack-ng -a2 -b [router bssid] -w [path to wordlist] /root/Desktop/*.cap
aircrack-ng -a2 -b [router bssid] -w [path to wordlist] /root/Desktop/*.cap
-a is the method aircrack will use to crack the handshake, 2=WPA method.
-b stands for bssid, replace [router bssid] with the BSSID of the target router, mine is 00:14:BF:E0:E8:D5.
-w stands for wordlist, replace [path to wordlist] with the path to a wordlist that you have downloaded. I have a wordlist called “wpa.txt” in the root folder.
/root/Desktop/*.cap is the path to the .cap file containing the password, the * means wild card in Linux, and since I’m assuming that there are no other .cap files on your Desktop, this should work fine the way it is.
-b stands for bssid, replace [router bssid] with the BSSID of the target router, mine is 00:14:BF:E0:E8:D5.
-w stands for wordlist, replace [path to wordlist] with the path to a wordlist that you have downloaded. I have a wordlist called “wpa.txt” in the root folder.
/root/Desktop/*.cap is the path to the .cap file containing the password, the * means wild card in Linux, and since I’m assuming that there are no other .cap files on your Desktop, this should work fine the way it is.
My complete command looks like this:
aircrack-ng –a2 –b 00:14:BF:E0:E8:D5 –w /root/wpa.txt /root/Desktop/*.cap
aircrack-ng –a2 –b 00:14:BF:E0:E8:D5 –w /root/wpa.txt /root/Desktop/*.cap
Now Press Enter.
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------
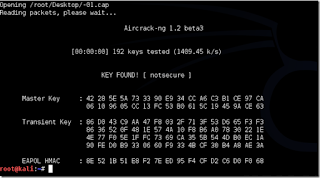
13. Aircrack-ng will now launch into the process of cracking the password. However, it will only crack it if the password happens to be in the wordlist that you’ve selected. Sometimes, it’s not. If this is the case, then you can congratulate the owner on being “Impenetrable,” of course, only after you’ve tried every wordlist that a hacker might use or make!
Cracking the password might take a long time depending on the size of the wordlist. Mine went very quickly.
If the phrase is in the wordlist, then aircrack-ng will show it too you like this:
The passphrase to our test-network was “notsecure,” and you can see here that aircrack found it.
If you find the password without a decent struggle, then change your password, if it’s your network. If you’re penetration testing for someone, then tell them to change their password as soon as possible.
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------
ENJOY !!!









Is there a way to hack WiFi via android?
ReplyDeleteAhh yes wibr+ could help you much !!!
Deletebro link for wordlist please
ReplyDeleteBro kina copy haney ko?? Afai lekha na. Mero blog weareanonymousa.blogspot.com le kaile ni copy+paste gardaina yaar. Timi le http://lewiscomputerhowto.blogspot.com/2014/06/how-to-hack-wpawpa2-wi-fi-with-kali.html yesko bata copy gare ko hai? Yesari ta lekhey ko majja nai aayena ni.
ReplyDeleteMake sure to check out this site if you want to do college homework right
ReplyDeletefilesidaly.com
ReplyDeleteWifi hacking ko lagi sasto adapter recommend
ReplyDeleteYalova
ReplyDeleteHatay
Muş
Bursa
Mersin
Wİİ
ankara parça eşya taşıma
ReplyDeletetakipçi satın al
antalya rent a car
antalya rent a car
ankara parça eşya taşıma
GİGXT
kocaeli evden eve nakliyat
ReplyDeletekilis evden eve nakliyat
bursa evden eve nakliyat
trabzon evden eve nakliyat
hakkari evden eve nakliyat
F7LXM
B37D8
ReplyDeletesohbet chat
burdur mobil sohbet et
ankara bedava sohbet siteleri
mersin yabancı görüntülü sohbet
telefonda kızlarla sohbet
rize parasız görüntülü sohbet
antep telefonda rastgele sohbet
edirne canlı sohbet odası
kocaeli parasız görüntülü sohbet uygulamaları
252B8
ReplyDeleteen az komisyon alan kripto borsası
shea butter sabunu
kucoin
binance
copy trade nedir
mobil 4g proxy
referans kimliği nedir
papatya sabunu
probit
1145D
ReplyDeletebibox
bitexen
kripto para kanalları telegram
bitcoin nasıl oynanır
paribu
bkex
probit
papaya meyvesi
bitcoin giriş
1D849
ReplyDeletesanal güvenilir şov
9FD69
ReplyDeletewhatsapp görüntülü şov
33DFB7D861
ReplyDeleteücretli şov
ücretli show
skype şov
görüntülü şov
whatsapp ücretli show
görüntülü show
telegram görüntülü şov
görüntülü şov whatsapp numarası
cam show
05772071CD
ReplyDeleteviagra
vega
green temptation
bufalo çikolata
degra
viga
geciktirici
yapay kızlık zarı
sinegra
5BC193E5EA
ReplyDeletedelay
geciktirici
sertleştirici
sildegra
bufalo içecek
fx15
telegram görüntülü şov
canli cam show
ücretli show
66FECD98EB
ReplyDeletestag
cam şov
sildegra
kaldırıcı
degra
ereksiyon hapı
whatsapp görüntülü show güvenilir
görüntülü şov whatsapp numarası
yapay kızlık zarı
294743BEB7
ReplyDeletesertleştirici
lady era hap
kaldırıcı hap
lifta
viagra
themra macun
sildegra
sinegra 100 mg
görüntülü şov
08A3A69105
ReplyDeletethemra macun
telegram görüntülü şov
lady era hap
sildegra
vigrande
vega
görüntülü show
whatsapp görüntülü şov
viagra
21763685D5
ReplyDeletetwitter düşmeyen takipçi
0016FD603E
ReplyDeletegüvenilir takipçi satın al
Footer Link Satın Al
War Robots Hediye Kodu
MFF Kupon Kodu
Türkiye Posta Kodu
İdle Office Tycoon Hediye Kodu
Türkiye Posta Kodu
Dude Theft Wars Para Kodu
Dragon City Elmas Kodu
34670B5786
ReplyDeleteEn İyi Telegram Farm Botları
Yeni Telegram Mining Botları
Telegram Para Kazanma Grupları
Telegram Mining Botları
Yeni Telegram Coin Kazanma Botları
A943CF7C53
ReplyDeletetürkiye'de en çok oynanan mmorpg oyunlar
sms onay
mobil ödeme bozdurma
takipçi satın alma
-
6B4B6710B6
ReplyDeletekiralık hacker
kiralık hacker arıyorum
kiralık hacker
hacker arıyorum
kiralık hacker
ReplyDeleteİnsan ruhunun derinliklerine inmek ve duygularını anlamak için en iyi yol, çeşitli kaynaklardan yararlanmaktır. Bu noktada, aşk kitapları, özellikle ilişkilerin ve sevginin farklı yönlerini keşfetmek isteyenler için oldukça faydalı olabilir. Her yeni kitap, aşkın farklı renklerini ve anlamlarını anlamamıza yardımcı olur. Bu nedenle, sevgiyle ilgili kitaplara zaman ayırmak, içsel dünyamıza yapacağımız güzel bir yolculuktur.